Do you encrypt your email? The vast majority of people don’t, mainly because they don’t understand the encryption process. Many assume that a firewall is all the protection they need, not taking into consideration the vulnerability of email messages once they leave their network. A firewall offers no protection for email entering or exiting a company’s network. Still, email encryption is something of a mystery for most. Encrypting email involves a pair of mathematically related cryptographic keys, one of which is public and the other private.
Public and private keys are created as a pair – meaning that encryption and decryption can only work within the confines of these two keys. A message encrypted with either of the two keys can only be read by using the other key in the pair. No other key can be used to decrypt the message.
So how does it work?
The technology that drives all of this is known as Public Key Infrastructure, or PKI. Anyone can use the Public Key, but only the holder of the Private Key can use this Private Key — it should never be shared.
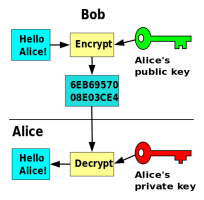
If someone wants to send me a private/encrypted email message, they simply use my Public Key to encrypt the message before sending. Since only I have the Private Key, only I can decrypt the message to see the original contents. I can also use this pair to prove that I am the sender of an email message. Let’s say that I want to send you an email message and you need a method of verifying that I am the sender. In this case, I’ll encrypt the message with my Private Key. You’ll get an encrypted email message. By successfully decrypting the message with the Public Key, you can be assured that I was the sender and that it isn’t someone masquerading as me.
Two operations can be combined to send private, encrypted messages that also verify the authenticity of the sender. I can use my Private Key to encrypt a message and then use your Public Key to encrypt it a second time. When you get the message, you’ll do the operations in reverse – first decrypt with your Private Key, then decrypt a second time with my Public Key.
How are public keys made public?
Key pairs are created and distributed by one of the many online entities that issue digital certificates, known as a certificate/certification authority, or CA. As a trusted third party, the CA provides certification for the ownership of the public key, entering it into a public directory. The private key is entrusted to the owner of the certificate and is not available to anyone other than the owner. Anyone seeking to send a secure message to the owner of the private key can access their public key via the public directory created by the CA, or by asking the intended recipient to forward their public key via email. There are also a number of public key directories online. You can search these directories by name or email address to discover the public key.
Regardless of the other security protocols you may have in place, email remains an area vulnerable to attack. The transparency of email is akin to placing your information on a postcard for the entire world to see. As we’ve covered in this space before, email is far from secure for sending sensitive information. Without encryption, messages can be intercepted, redirected, and viewed by unauthorized individuals. Encryption provides a measure of security for your email communications. Keep in mind, however, that once decrypted at either end, the information contained within can still be passed along without re-encrypting.
Do you encrypt your email? Why or why not? Let us know!
For more information: https://casecurity.org/

